Someone just walked away with $4 million in IRYS tokens. They didn’t hack anything. They simply gamed the airdrop using 900 wallet addresses.
This week’s IRYS token launch highlights a persistent problem in crypto. Projects keep using airdrops to decentralize ownership. But coordinated actors keep finding ways to capture massive portions of the supply before regular users get a chance.
The Numbers Tell a Troubling Story
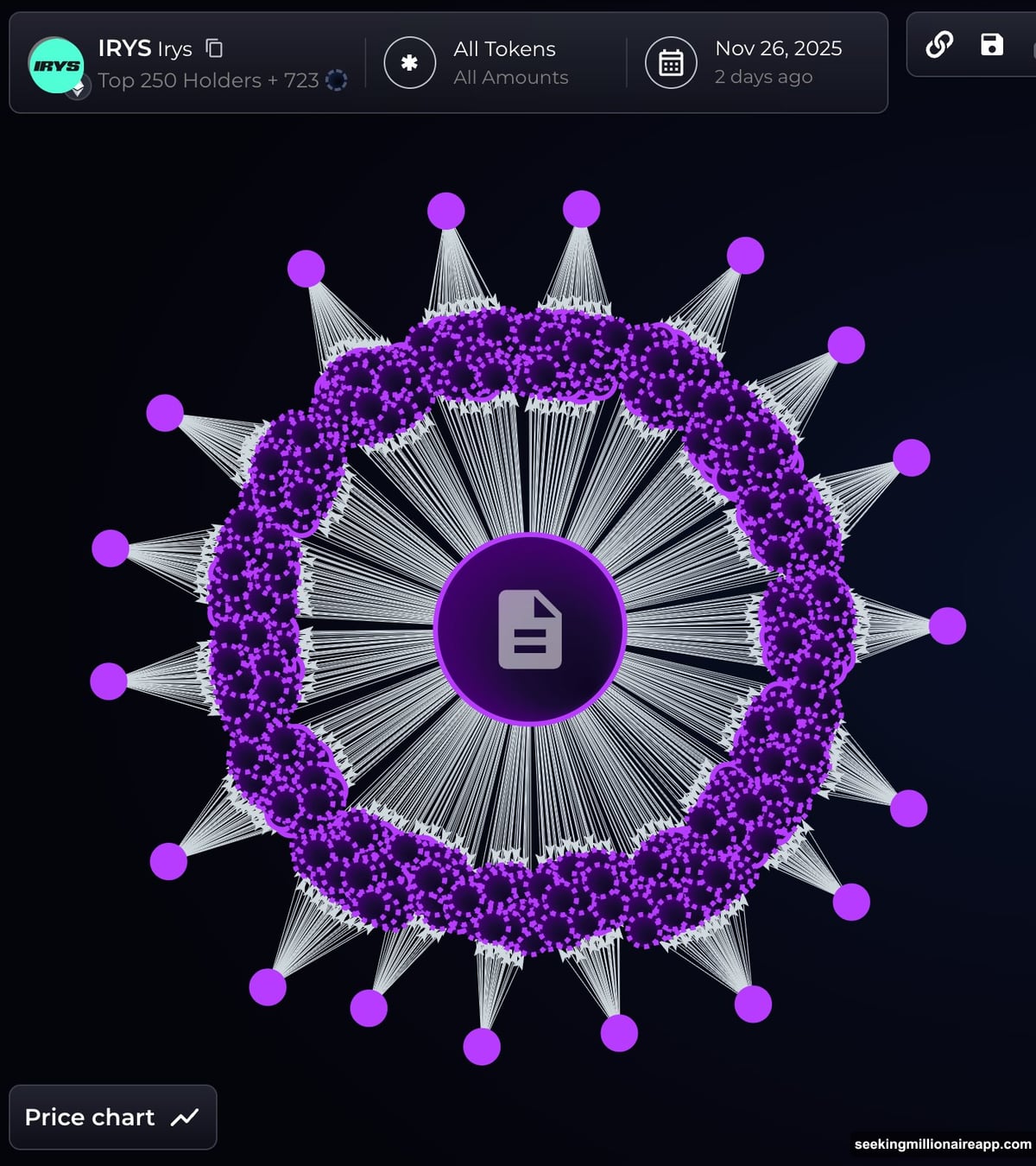
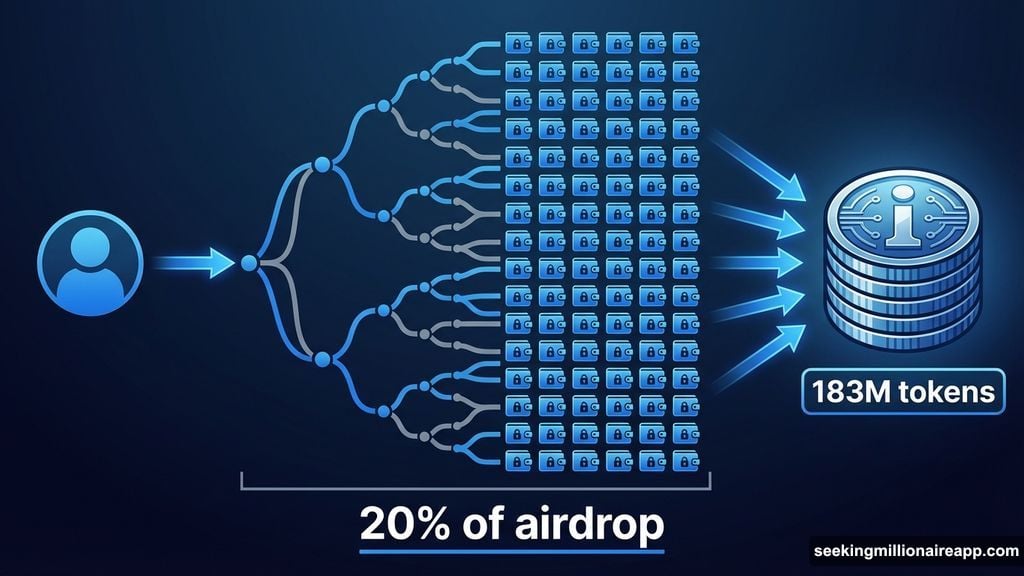
Blockchain analytics firm Bubblemaps identified roughly 900 wallets that claimed about 20% of the total IRYS airdrop allocation. The cluster moved approximately $4 million worth of tokens through a coordinated network.
Here’s what makes this suspicious. None of these 900 addresses showed any prior on-chain activity. They appeared specifically for this airdrop. Then they immediately started consolidating funds.
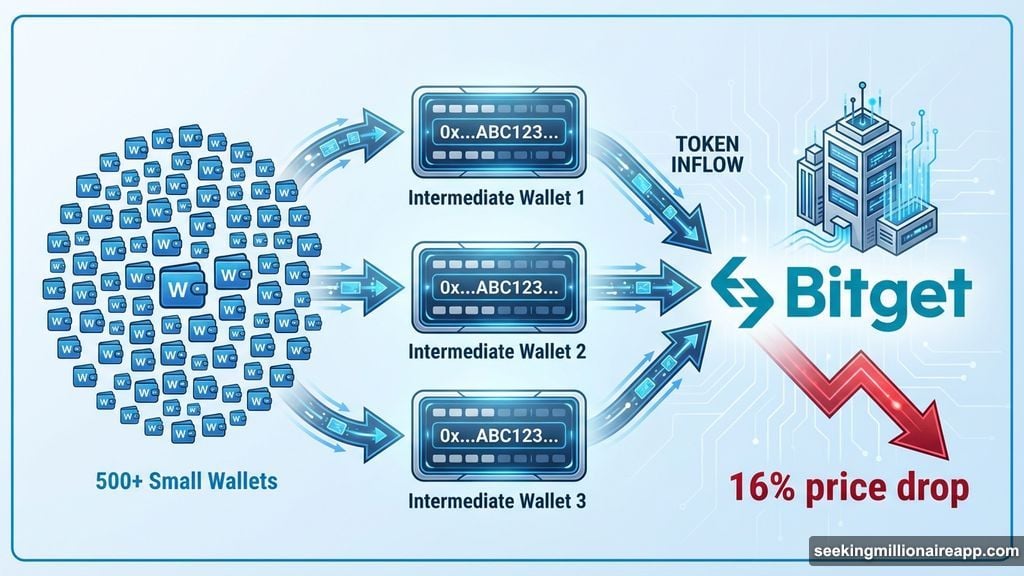
About 500 of the identified wallets transferred their IRYS tokens to intermediary addresses. From there, the tokens flowed to Bitget exchange. That pattern suggests preparation for immediate liquidation.
The IRYS team distributed 400 million tokens total through the airdrop. That represents 8% of the project’s entire supply. The goal was network decentralization. Instead, one entity captured 183 million tokens through script-generated wallets.
Market Impact Hit Fast
IRYS price dropped 16% in the 24 hours following these revelations. The token traded near $0.032 at press time. That’s not surprising when one entity controls 20% of circulating supply and appears ready to dump.
Plus, the sell pressure hasn’t fully materialized yet. Those tokens sitting on Bitget represent a sword hanging over existing holders. Nobody knows when that entity might trigger a massive sell order.
Meanwhile, IRYS launched on major exchanges including Coinbase and Binance this week. The project raised over $13 million from venture capital investors. It markets itself as “on-chain AWS” for data storage and smart contracts.
But that professional backing didn’t prevent the airdrop exploit. So the incident raises questions about how thoroughly projects vet their distribution mechanisms before launch.
Sybil Attacks Keep Working
This pattern keeps repeating across crypto projects. One entity recently claimed 60% of the aPriori airdrop using 14,000 addresses. Another grabbed $170 million from the MYX airdrop with 100 freshly funded wallets.
The technique is straightforward. Generate hundreds or thousands of wallet addresses. Fund them with small amounts to meet participation requirements. Claim the airdrop across all wallets. Consolidate and cash out.
Projects struggle to detect these coordinated clusters before distribution. Blockchain analytics firms can identify suspicious patterns after the fact. But by then, the damage is done.
Bubblemaps noted they found no evidence linking the IRYS team to the wallet cluster. That’s good news. But it doesn’t solve the underlying problem.
Why Airdrops Keep Failing
Airdrops aim to decentralize token ownership and reward early supporters. In practice, they often concentrate tokens in the hands of professional airdrop farmers.
Think about the incentives. If you can generate 900 wallets and capture $4 million in tokens, you absolutely will. The barrier to entry is just technical knowledge and some upfront capital for wallet funding.
Regular users claim tokens from one or two wallets. They participate because they used the protocol. Meanwhile, coordinated actors claim tokens from hundreds of wallets purely for profit.
The result? Early liquidity events benefit short-term actors more than long-term holders. That dynamic undermines the stated goal of building sustainable community ownership.
Better Solutions Exist But Rarely Get Used
Projects could implement stronger Sybil resistance. Identity verification helps but conflicts with crypto’s privacy ethos. On-chain reputation scores work but exclude newcomers. Proof-of-humanity systems exist but add friction.
Most projects choose convenience over security. They want maximum participation and headlines about large airdrop numbers. So they skip robust filtering mechanisms.
Then they act surprised when professional farmers capture outsized allocations. But this outcome is entirely predictable given the design choices.
Some projects are experimenting with alternative distribution models. Staggered vesting schedules reduce immediate sell pressure. Requirement proofs based on genuine protocol usage help filter out farmers. Lottery systems introduce randomness that makes coordination harder.
But these approaches remain the exception. Most projects stick with simple snapshot-based airdrops despite repeated evidence of their vulnerability.
The Bigger Picture
This IRYS incident isn’t unique. It’s emblematic of structural challenges across permissionless crypto ecosystems. Minimal identity checks and unrestricted network access make coordination attacks trivial.
Projects face a difficult tradeoff. Tighter security measures might prevent exploits but also create barriers for legitimate users. Looser requirements enable broader participation but invite abuse.
Right now, the balance tilts too far toward convenience. That needs to change. The current approach subsidizes professional airdrop farmers at the expense of genuine community members.
Token launches matter. They set initial distribution patterns that persist throughout a project’s lifetime. When one entity controls 20% of circulating supply from day one, that fundamentally shapes price dynamics and governance outcomes.
IRYS holders are living with those consequences right now. They’re watching $4 million in tokens potentially flood the market while their own holdings lose value. That’s not decentralization. That’s just poor distribution design creating predictable exploitation.