A criminal group thought they could shake down one of the world’s biggest crypto exchanges. They were wrong.
Kraken confirmed this week that two separate insider incidents exposed limited client data through support staff access. Shortly after, a criminal group used that exposure as leverage, threatening to release internal videos showing client information unless the exchange paid up. Kraken refused, called law enforcement, and went public with the whole story.
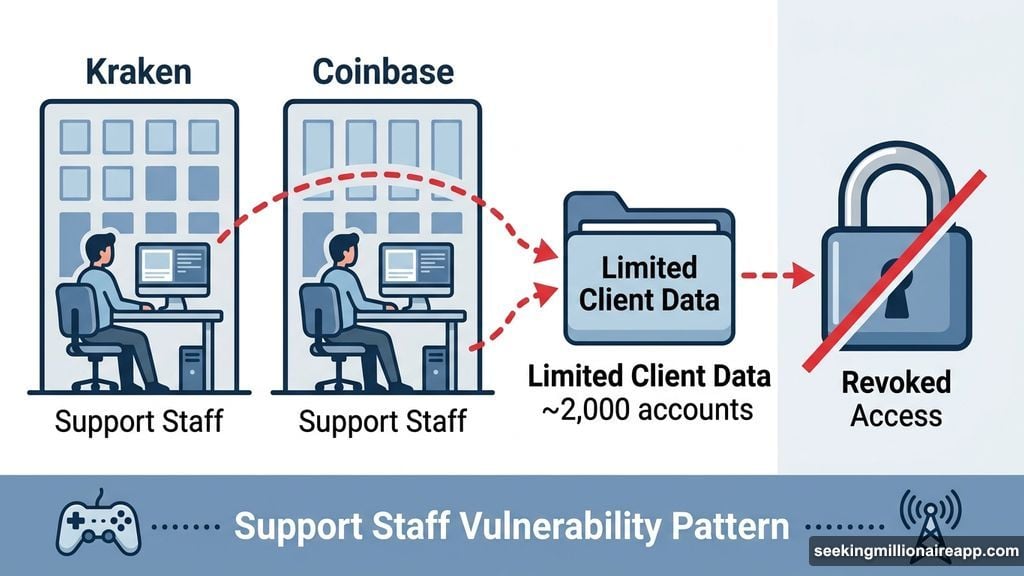
Insider Access Hit Support Systems, Not Trading Infrastructure
The incidents involved support staff who gained unauthorized access to limited client data. Kraken’s Chief Security Officer, Nick Percoco, was direct about the scope. No trading systems were compromised. No funds were touched. The exposure stayed within support infrastructure.
About 2,000 client accounts were potentially viewed during both incidents, representing roughly 0.02% of Kraken’s total user base. That’s a small fraction, but even small breaches become serious when criminals get involved. Support access was revoked quickly after each alert, and affected users received notifications.
Percoco confirmed the extortion attempt publicly. “We are currently being extorted by a criminal group threatening to release videos of our internal systems with client data shown if we do not comply with their demands,” he wrote.

Kraken Refused to Pay, Then Called the Feds
Some companies quietly pay extortion demands to make problems disappear. Kraken chose the opposite approach.
The exchange refused to negotiate and immediately escalated to federal law enforcement across multiple jurisdictions. According to Percoco, investigators have gathered enough evidence to pursue identification of everyone involved. “We are actively working with federal law enforcement across multiple jurisdictions to pursue all individuals involved and bring them to justice,” he added.
This isn’t just about Kraken defending its reputation. Refusing to pay sends a clear signal to criminal groups that crypto exchanges won’t become easy targets. Every payout encourages the next attempt.
This Mirrors the Coinbase Breach Pattern
If this story sounds familiar, that’s because it is. Coinbase dealt with a nearly identical situation in 2025, where bribed overseas support agents leaked customer information to bad actors.
Both cases share the same fingerprint. Support staff access exploited through bribery or manipulation, no core systems breached, client funds left untouched, and both exchanges refusing to comply with extortion demands while cooperating with law enforcement. Security teams across the crypto sector have responded by tightening access controls and boosting monitoring of support staff activity.
Similar tactics have appeared in gaming and telecom industries too, according to industry reports. This isn’t a crypto-specific problem. It’s a support staff vulnerability problem that shows up wherever customer data has value.
The Offshore Hiring Debate Heats Up
Kraken’s response sparked a pointed conversation in comment sections and forums. Some users argued that hiring support staff in certain regions increases bribery risk.
“Why don’t you hire people from developed countries? I won’t put my money on a platform that I have to hope for their third world support staff to not get bribed by criminals to expose my data,” one user wrote bluntly.
Kraken hasn’t directly addressed those comments. Instead, the exchange pointed to access controls as the primary safeguard, not employee location. That answer didn’t fully satisfy critics, but it reflects a real tension in the industry. Global support operations help exchanges scale and reduce costs. But they also create security challenges that technical controls alone can’t always solve.
What Kraken’s Response Gets Right
Extortion attempts work best when victims stay quiet and pay fast. Kraken did neither.
Going public immediately removes the criminal group’s leverage. If the videos get released now, they reveal information Kraken already disclosed. The threat loses most of its power. Plus, coordinating with law enforcement across multiple jurisdictions creates genuine legal risk for the attackers, not just the exchange.
The 2,000 affected users represent real people whose data got caught in the middle. Notifying them quickly was the right call, even if the news is uncomfortable. Trust in crypto exchanges depends heavily on transparency during incidents like this, and Kraken handled the disclosure cleanly.
The harder question is what happens next. Both Kraken and Coinbase faced similar attacks within a short window. That pattern suggests organized groups are specifically targeting crypto exchange support operations, probing for weak points in human systems that technical defenses can’t fully cover. The industry’s response to this growing threat will matter far more than any single incident.
