Fake emails from Robinhood’s own email address landed in customer inboxes Sunday evening. And the scary part? They looked completely legitimate.
Robinhood confirmed the incident was a phishing attempt that abused its account creation flow. Customer accounts and company systems weren’t breached, but the attack was sophisticated enough to fool standard email security checks. Here’s what you need to know.
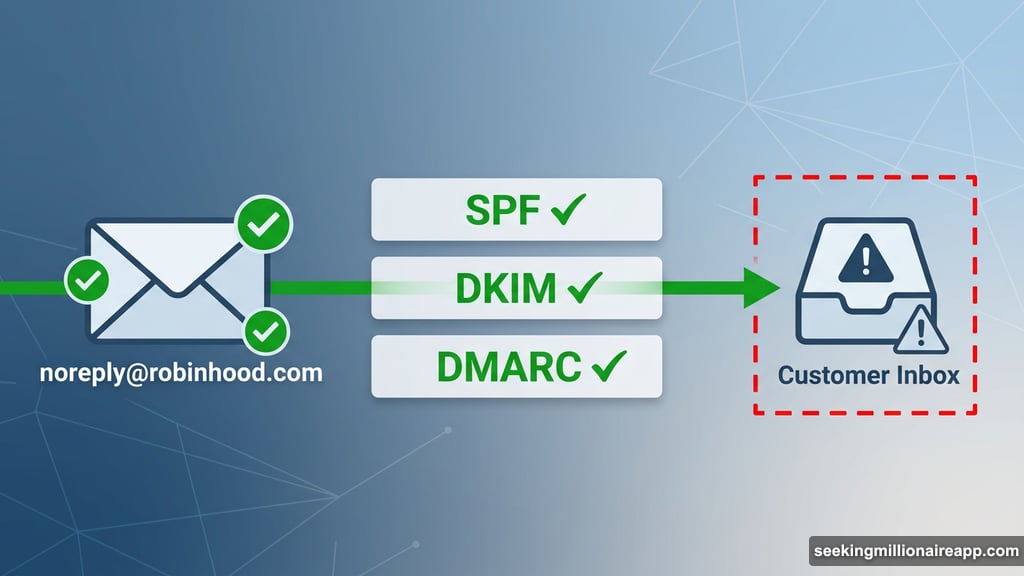
Phishing Emails Passed SPF, DKIM, and DMARC Authentication
This wasn’t your typical poorly spelled spam email. The fraudulent messages came from [email protected] with the subject line “Your recent login to Robinhood.”
One Robinhood customer downloaded the raw email file and checked the technical authentication headers. The results were alarming. The email passed SPF, DKIM, and DMARC verification — three industry-standard security checks that email providers use to confirm a message is genuinely from who it claims to be.
In plain terms, that means even sophisticated email filters would flag this message as legitimate. Because, technically, it came from Robinhood’s own infrastructure.

Attackers Injected a Phishing Payload Into Real Robinhood Emails
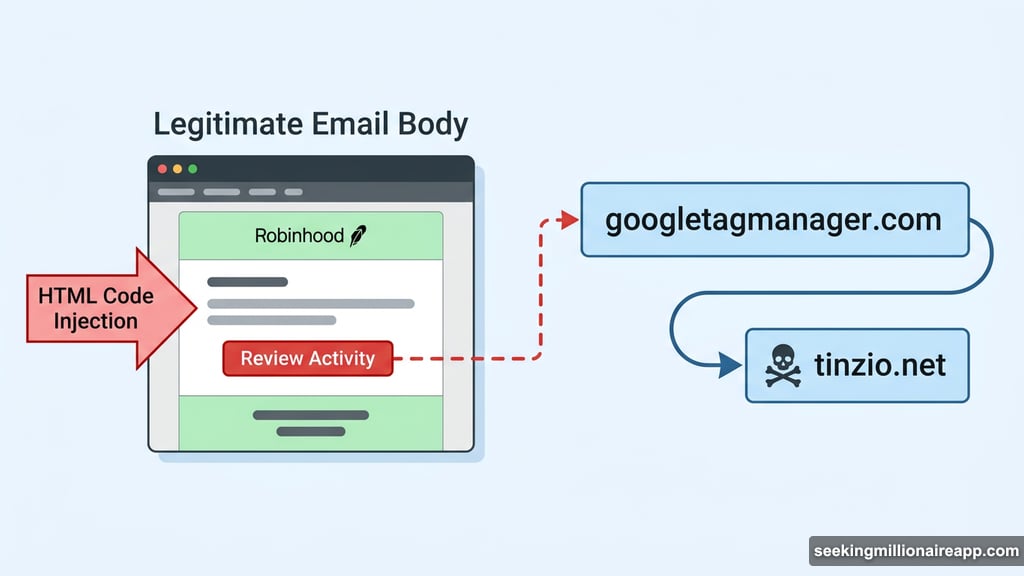
So how did a real Robinhood email become malicious? Attackers injected HTML code directly into the legitimate email body.
That injected code added a “Review Activity” button to the message. Clicking it redirected users to a suspicious domain called tinzio.net, routed through googletagmanager.com to disguise the final destination. The top half of the email looked exactly like a normal Robinhood security notification. The phishing payload was buried inside.
David Schwartz, CTO emeritus at Ripple, flagged the campaign publicly. He warned that the messages appeared to originate from Robinhood’s actual email infrastructure, not an external spoofed account. “I’m not sure exactly what’s going on, but it seems like these emails were somehow injected into Robinhood’s actual email infrastructure at some point,” he said.
Robinhood has not yet explained precisely how attackers accessed the account creation flow or injected content into outgoing messages. The company also hasn’t confirmed how many customers received the fraudulent email.
What Robinhood Is Telling Customers to Do Right Now
Robinhood’s help account posted guidance on X shortly after the incident surfaced. The company’s advice is straightforward and worth following immediately if you received this email.
First, delete the message and don’t click anything inside it. Second, contact Robinhood support only through the official app or website — never through links in the email itself. Third, if you interacted with the email at all, change your password right away.
Robinhood also strongly recommends rotating your two-factor authentication (2FA) setup and reviewing recent device activity on your account. Two-factor authentication adds an extra verification step when logging in, making it much harder for attackers to access your account even if they have your password.
The good news is that Robinhood confirmed customer balances and personal data remained untouched. This attack targeted credentials, not stored funds.
HOOD Stock Held Steady Despite the Scare
Markets mostly shrugged at the news. Robinhood stock (HOOD) traded near $84.71 on Monday morning, up 1.40% on the day. The stock did record pre-market losses of about 0.3%, suggesting some brief jitters after the Sunday evening incident surfaced.
But the stock’s quick recovery reflects investor confidence that no actual breach occurred. No customer data was stolen. No funds were drained. The attack exploited a process vulnerability rather than cracking Robinhood’s core systems.
Still, the incident raises uncomfortable questions. If attackers can inject phishing payloads into emails that pass every major authentication check, what does that mean for how we trust financial emails going forward?
Why This Attack Should Make Everyone More Cautious
The unsettling reality is that this phishing campaign beat the email authentication tools most people rely on. SPF, DKIM, and DMARC exist precisely to prevent fake emails from reaching your inbox. This attack worked around all three by using Robinhood’s own infrastructure as the delivery mechanism.
That flips the usual advice on its head. Normally, you check that an email comes from a legitimate domain. This email did come from a legitimate domain. The attack was the content inside, not the sender address.
So the smarter habit going forward is this: never click security-related links inside any financial email, even if it looks perfect. Instead, open your banking or brokerage app directly. Navigate to any flagged activity from there. It takes ten extra seconds and eliminates the risk entirely.
Robinhood’s transparency here is worth acknowledging. The company confirmed the incident quickly, posted clear guidance, and was honest that it hadn’t yet identified exactly how attackers accessed the account creation flow. That kind of openness matters during a security incident.
What matters now is that affected customers follow the recommended steps immediately. Change your password, update your 2FA, and check your recent device activity. Don’t wait on this one.
